...
- Welcome & Introductions
- EFWG Community Topics & Announcements
- Presentation from Trinsic: "Solving Governance in SSI Ecosystems with Trust Registries"
- Q&A / Discussion
- Ecosystem white paper passed by all members present with no dissent
- Tomislav Markovski presenting Ecosystem Governance and SSI - Trust Registries
- Importance of Governance in Identity - to provide a layer of trust in an open ecosystem
- need to protect authentic data
Multiple approaches to Governance - who provides the root of trust- First three - are fairly decentralized methods
- last two more decentralized model
- Trust Registry
- answers if an ecosystem participant has authority to act according to governance framework
- practical problem - how for all verifiers maintain lists of all authorized members in a given ecosystem
- cross ecosystem trust establishment - different ecosystems can identify other ecosystem's trust registries that they also trust
- Participants don't have to trust ecosystem itself, but that data providence is trusted
Types of trust registries- Thinking about them in term of technical solutions
- Not just a list of members, can be other types as well
- Trinsic has done work with centralized trust registries
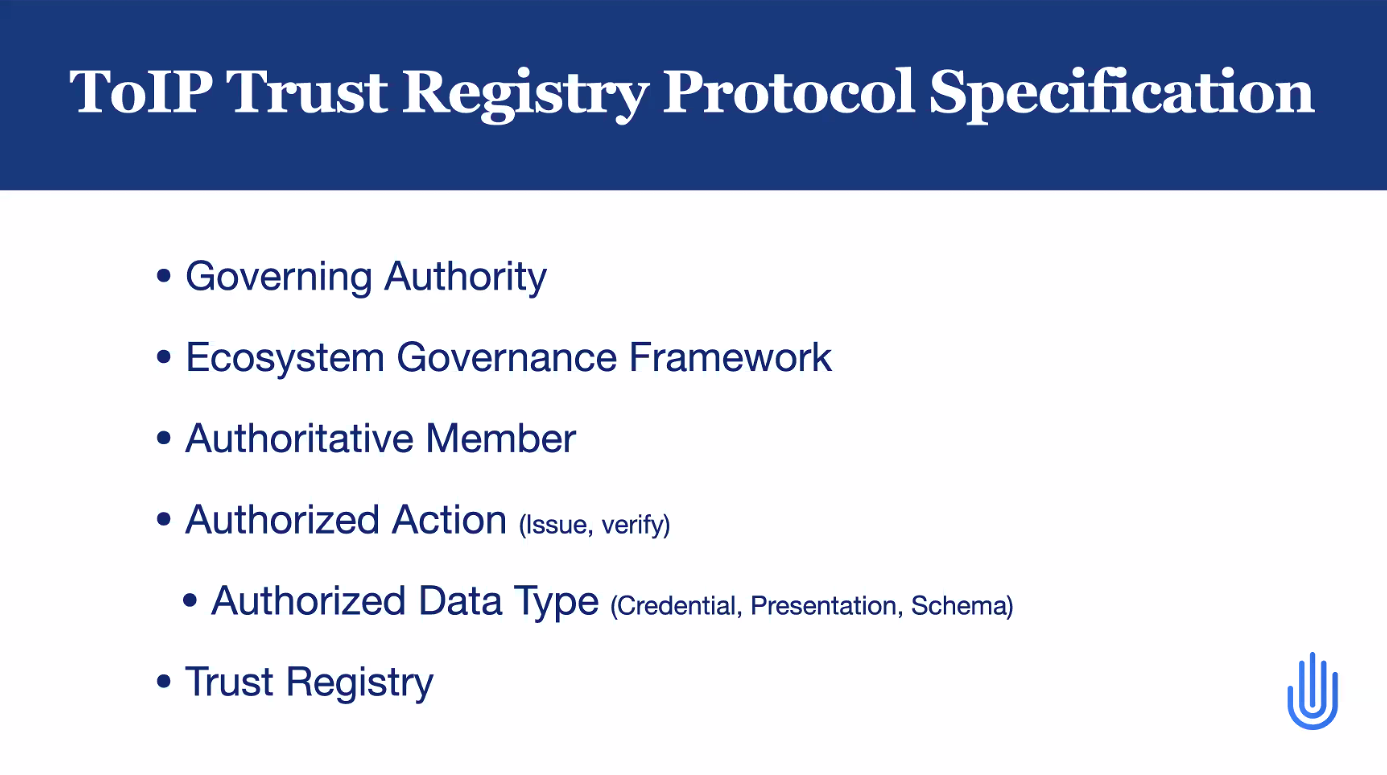
- ToIP trust registry protocol specification
Related efforts- Trust Establishment currently under early development https://identity.foundation/trust-establishment/
- TRAIN- registering definitions of credential schemas https://essif-lab.eu/essif-train-by-fraunhofer-gesellschaft/
- Trinsic solution
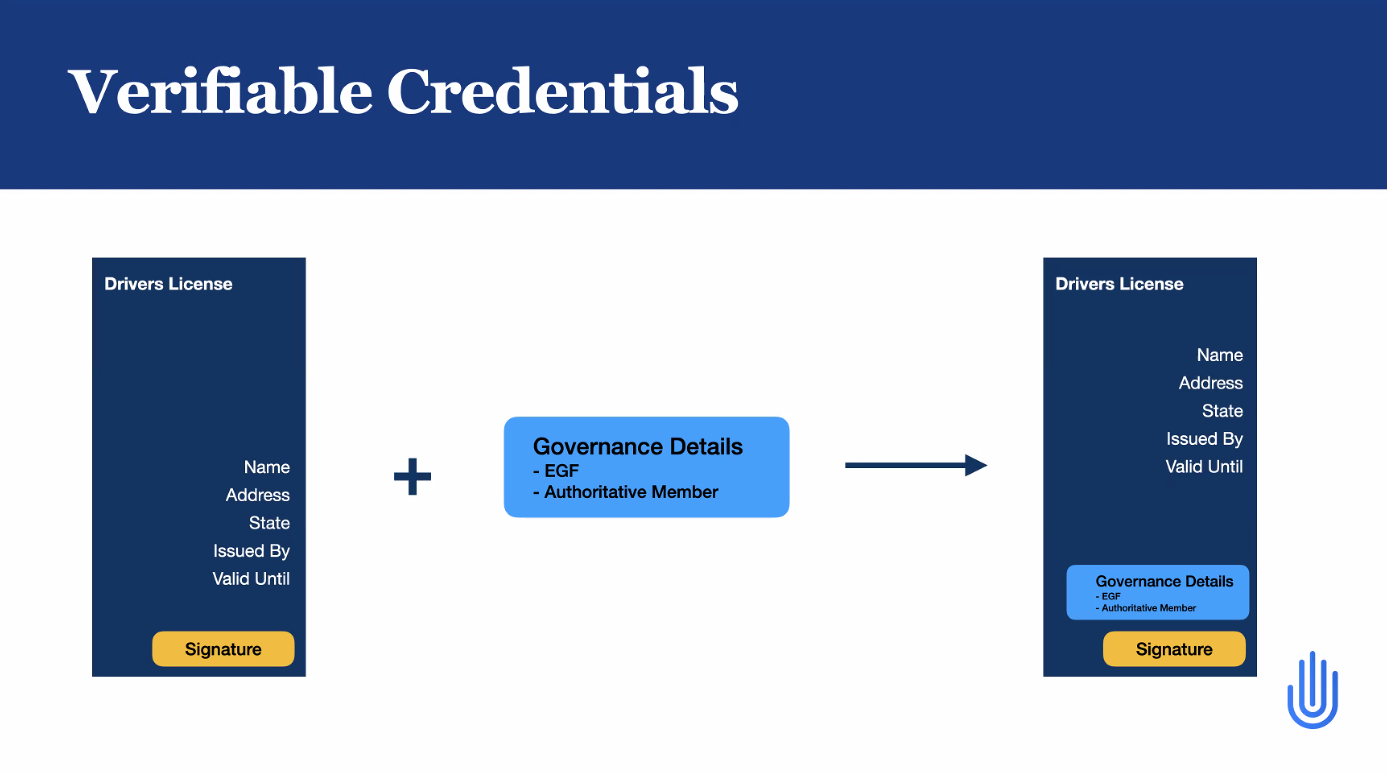
- the ToIP trust registry specification merged with verifiable credentials
- No information coded in credential how valid is the credential
- in an open ecosystem can have anyone issuing credentials
- add the governance information to the credential for referencing.
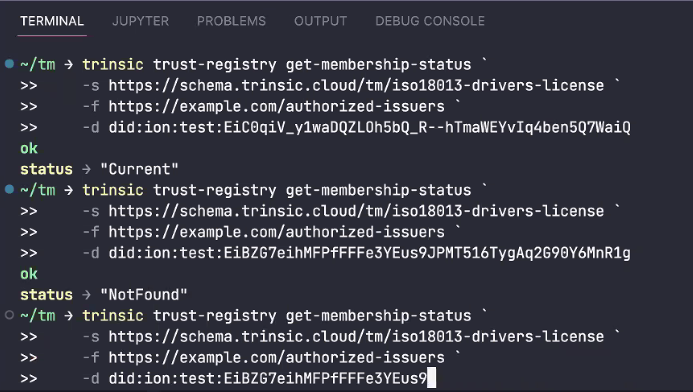
- Can validate the issuer ID but also the governance associated with it.
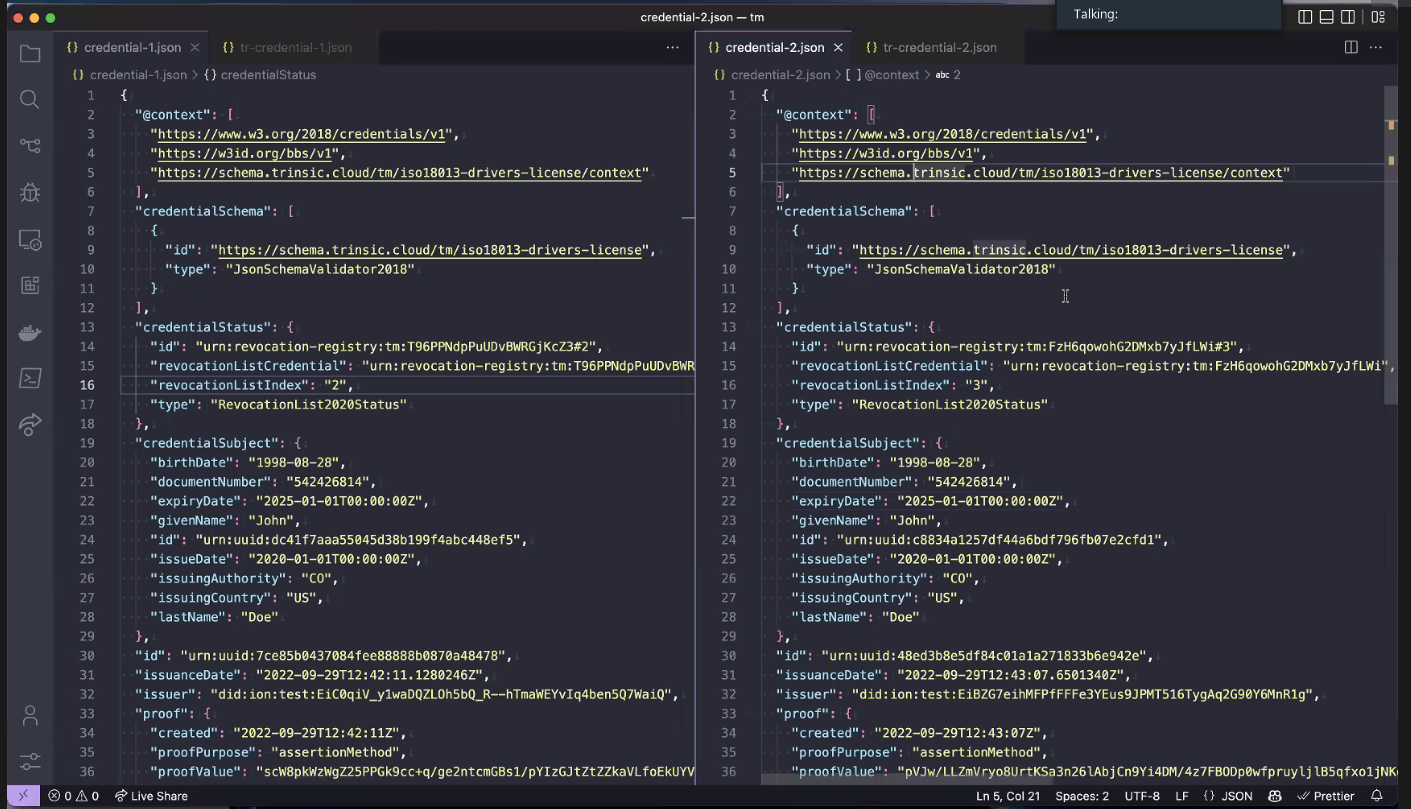
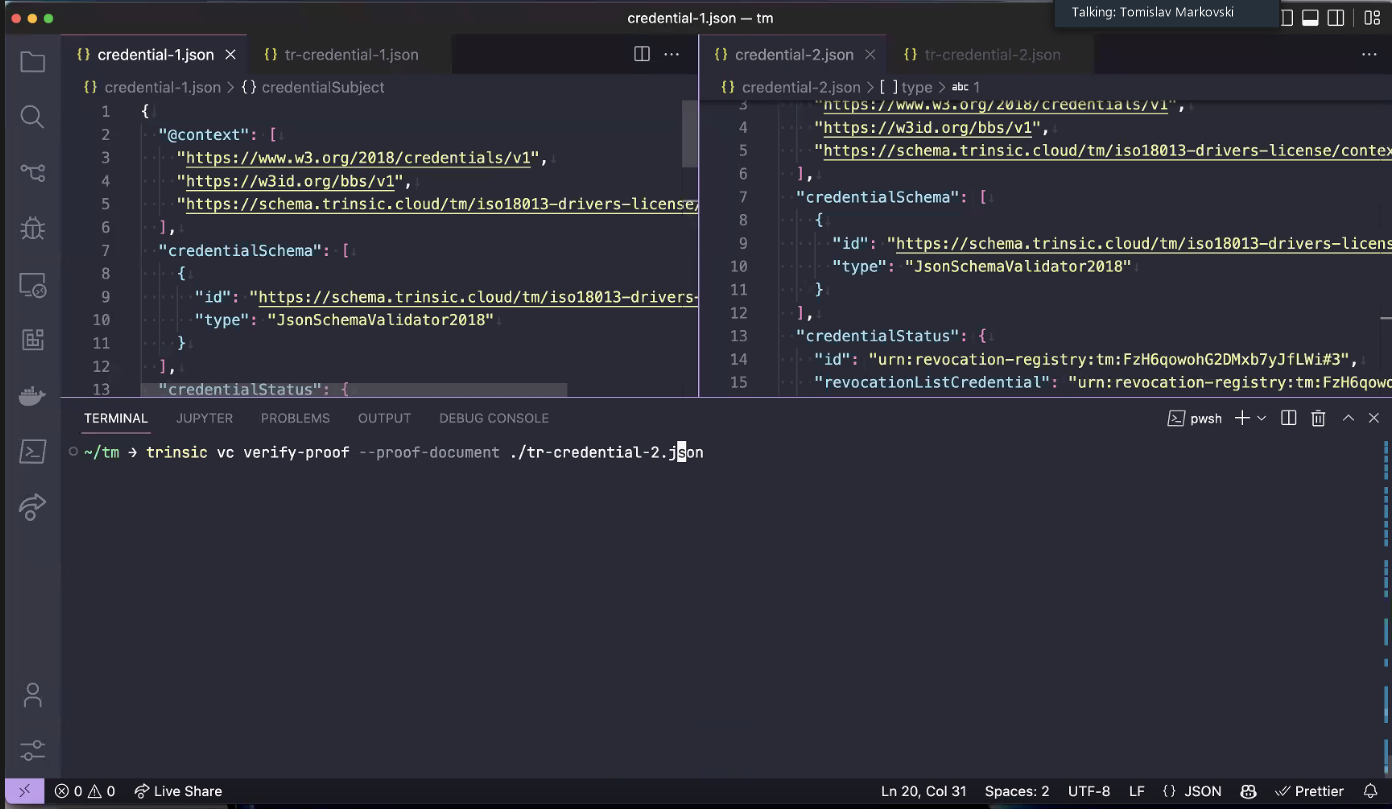
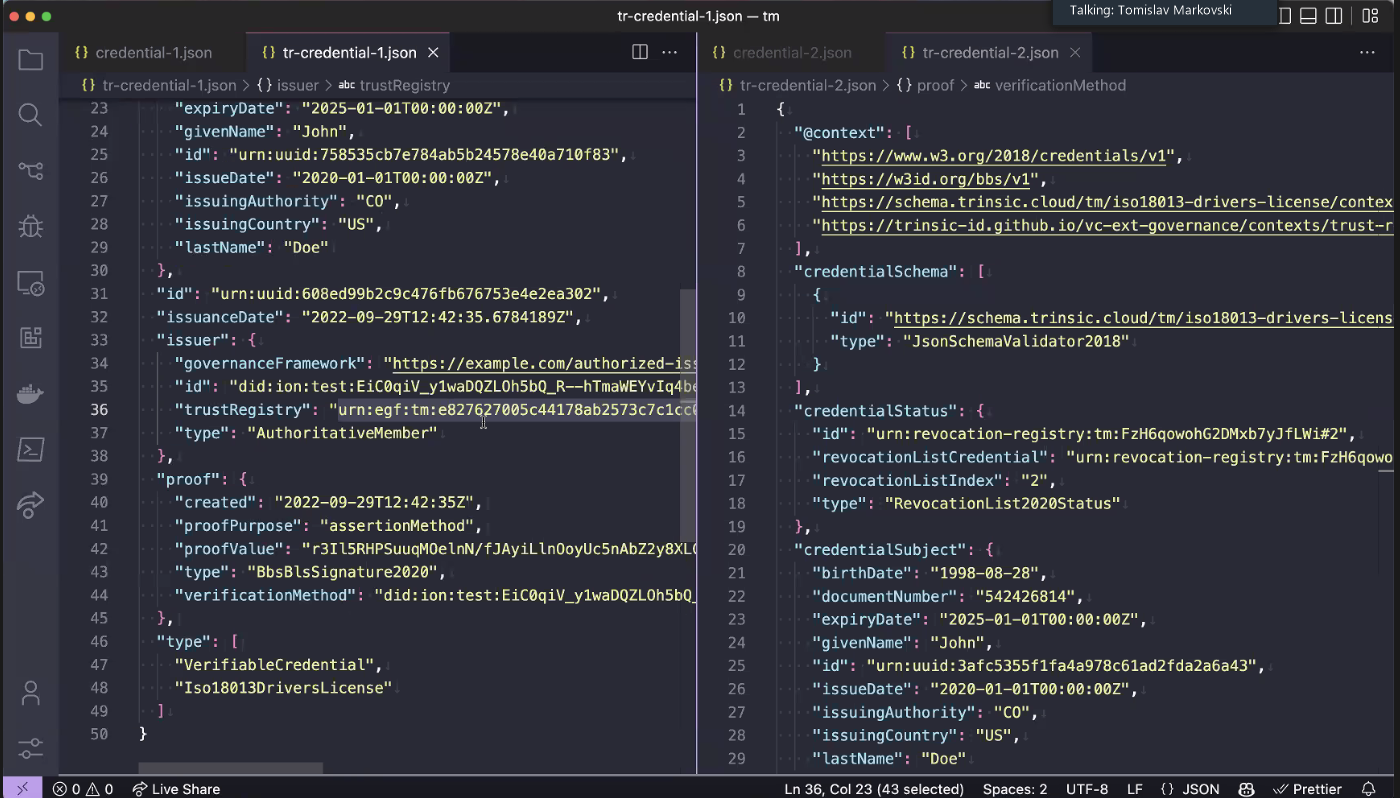
- Demo - no yet in production, CLI demo,
- two VC demos, good and bad actor issuers and with and without governance for verification
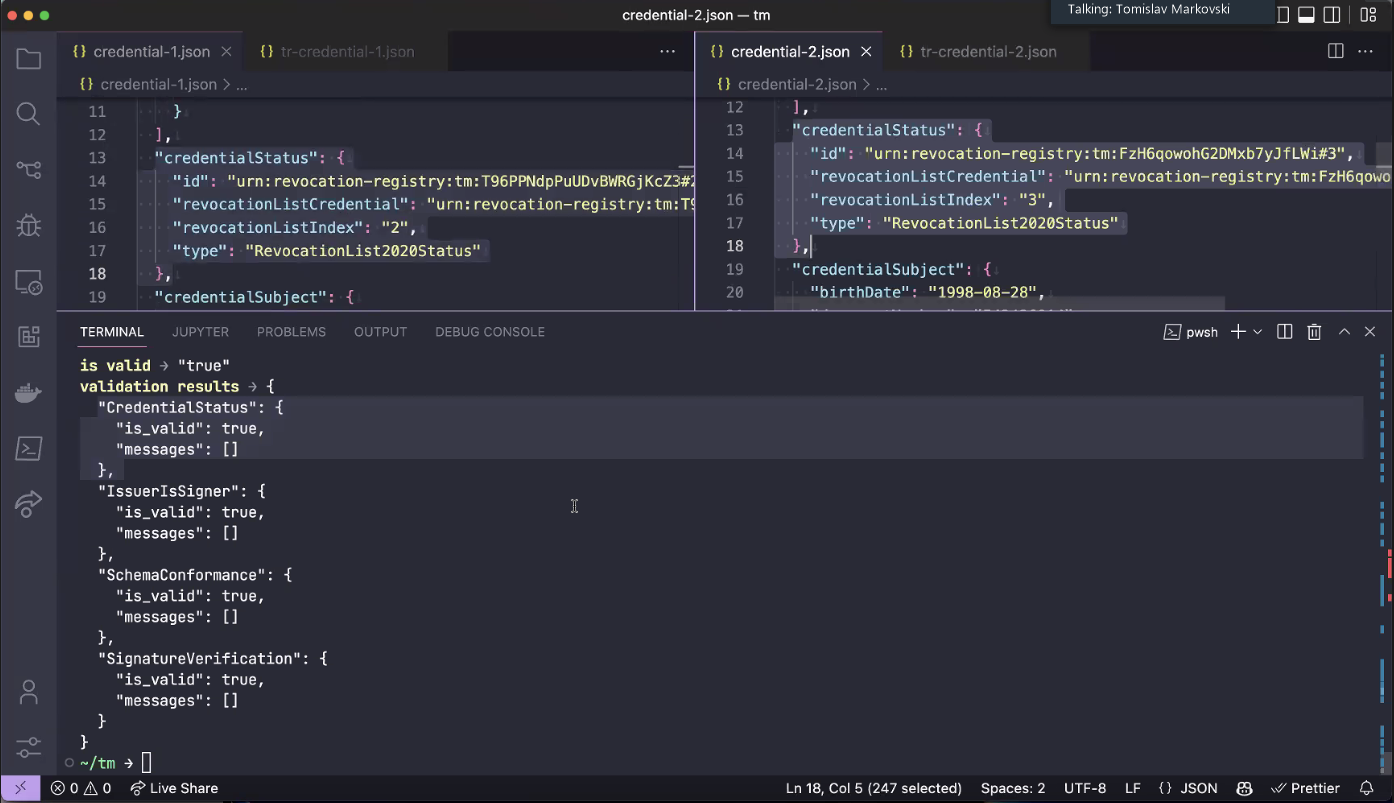
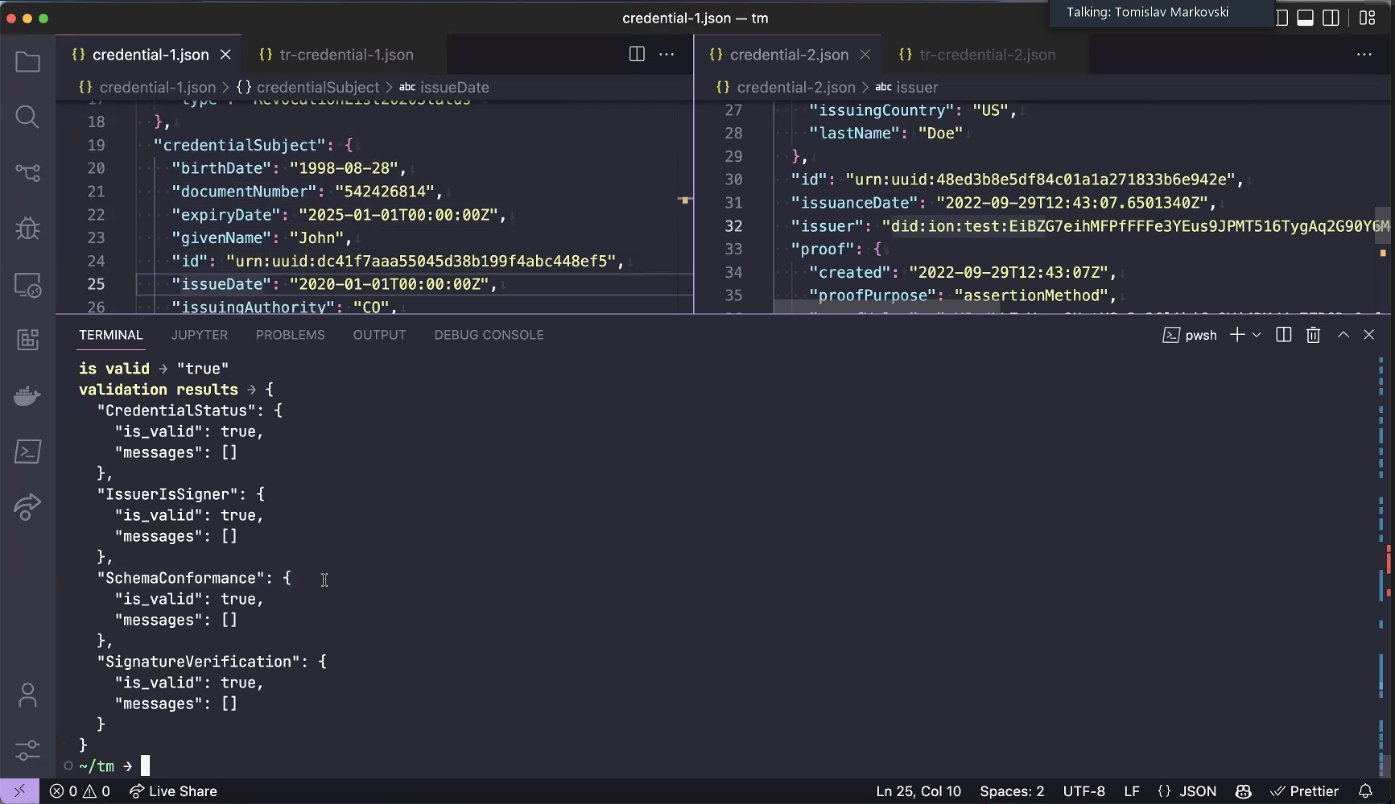
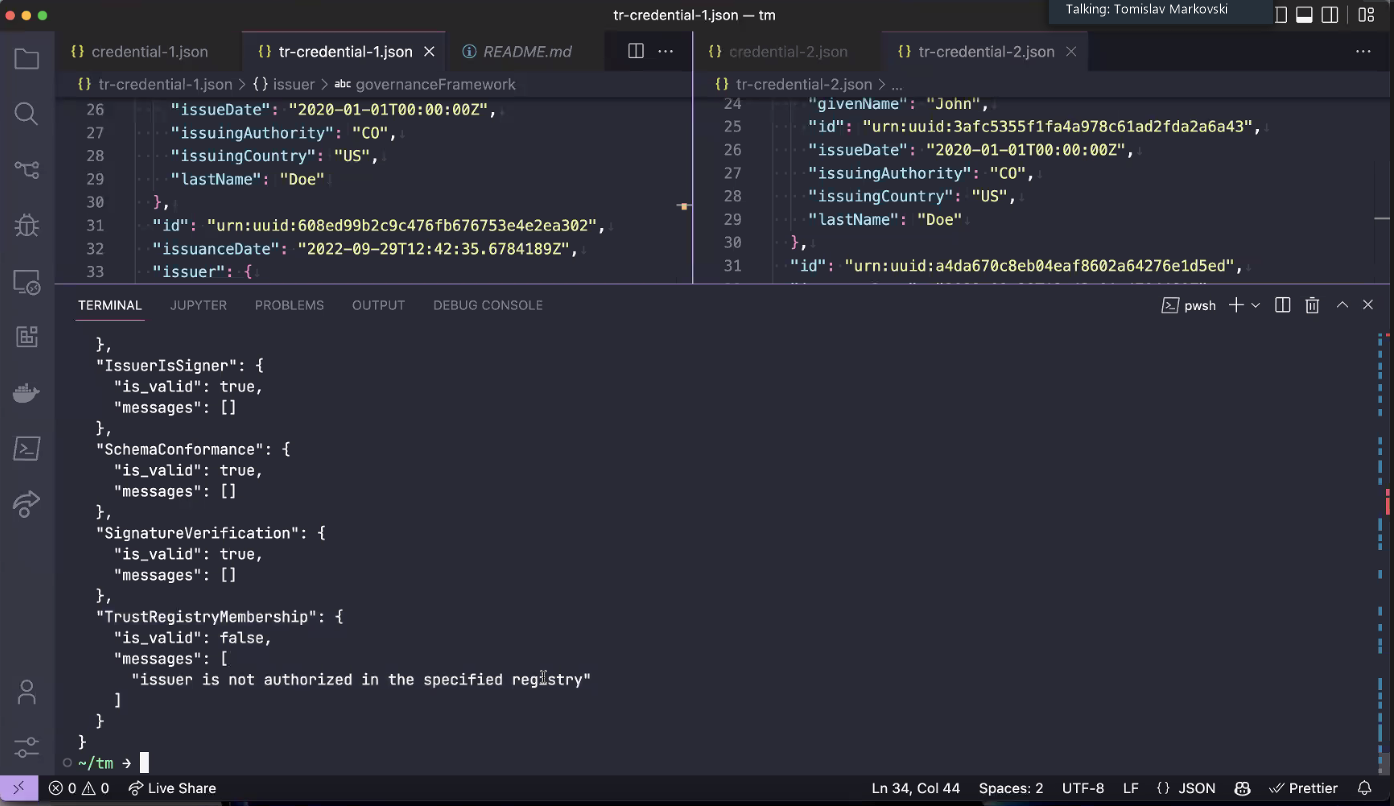
- Demo on good actor first confirms credentials are valid, not revoked, schema conforms, valid issuer, and signature verified for both good and bad actors.
- All the checks pass because there is nothing wrong with both credentials.
- How do you know? Trust Registry solves this.
- Issue a credential with governance information encoded.
- There is an issuer field extension to the VC ,in the credential - not just the issuer DID. It includes claims of which governance framework and trust registry it belongs to.
- Now verification doesn't work for the bad actor because the trust registry membership fails (an additional check)
- Is there a list of EFGs and how do you discover them?
- No list of Ecosystem Governance Frameworks that exist that someone maintains
- Presumably it would be published on the website
What controls are required to prevent bad actors from adding records to trust registries?
Depends on security and design of trust registries -it depends on who manages the registry.
How will a standard schema be adopted for a given verifiable credential? Who drives it?
- Community, adoption, large corporations, open standards e.g. mDL
- Schemas - will be interesting how communities adopt schemas. Centralizing and standardizing will develop
Q. What's next for your project? Where is it going in the next six months or so?
- Better management tools.
- Adding privacy preserving trust registries, especially based on accumulators (useful also for revocation)
- Q. What do you hope to learn early in deployment?
- How customers use the product
Q. How much do various credential ecosystem parties have to do to extend what they do to include the registry?
- minimal - current trust registry is membership based, just add and remove members
- extensions possible
- e.g. can be member of multiple governance frameworks/trust registries
- Concerns - correlation attacks, e.g. info leaks from the issuer identity
Presentation Files
- Google Slides
...